
Safewhere Identify 5.15
We are happy to announce the release of Safewhere Identify 5.15. In this topic, you will find the release notes for all new features and bug fixes in version 5.15, as well as any breaking changes when upgrading from previous versions.
New features and improvements
Safewhere Identify
MariaDB Provider support
We are excited to announce that Identify now supports MariaDB, an open-source SQL technology. This integration allows customers to leverage the benefits of an open-source solution, providing a more cost-effective alternative and making Identify even more competitive. Operating Identify with MariaDB brings the advantage of reduced operational expenses.
While ensuring that all key features work properly, our team is committed to addressing and resolving any identified issues promptly. The goal is to ensure a seamless experience for all users adopting MariaDB with Identify.
You can only create new Identify instances using MariaDB. Upgrading existing instances from MSSQL server to MariaDB is not supported.
Configuring MariaDB with Identify is straightforward. We have provided comprehensive guidelines for various environments, whether you are setting up MariaDB locally, on a Linux system with Docker, or in the Azure cloud. Visit the Getting started with Identify using MariaDB guidelines for step-by-step instructions to get started.
OAuth 2.0 SAML Bearer grant type support
We have implemented the RFC7522 – OAuth 2.0 SAML Bearer grant type, enabling clients to request access tokens using trusted SAML tokens. This powerful combination enhances security and provides a standardized approach to secure token-based authentication and authorization.
To leverage the power of OAuth 2.0 SAML Bearer grant type support, you can find more details on this topic.
OAuth 2.0 JWT Bearer grant type support
We have implemented the RFC7523 – OAuth 2.0 JWT Bearer grant type, enabling clients to request access tokens using signed JSON Web Tokens (JWT). This powerful integration allows for a secure and standardized approach to obtaining access tokens for API calls and ensures the privacy and integrity of the transmitted data.
To leverage the power of OAuth 2.0 JWT grant type support, you can find more details on this topic.
Standardize the index names on the Identify database
In version 5.15, we have corrected inconsistent index names and also renamed all existing indices that did not have the correct names on the Identify instances.
You can find the list of all added indices on the new Identify instance here.
Identify Admin and load-balancing
Previously, the Identify Admin used ephemeral in-memory data protection keys to secure its cookies. When Identify is deployed in a redundant setup, this in-memory mode requires sticky sessions to function properly. Consequently, deployments that do not use sticky sessions and rely on SQL Session state experienced invalidated sessions when users logged in with one server but were routed to another server afterwards.
We have addressed this issue by switching from ephemeral in-memory data protection keys to storing keys in the Identify database. This change has resulted in several important updates.
Firstly, the Identify Admin now needs to read the keys from the Identify database, requiring connection strings to be configured in its appsettings.json file. For security purposes, we encrypt those connection strings using the servers’ machine keys, similar to how connection strings of the Runtime application are encrypted.
Secondly, the Identify Admin utilizes Asp.Net Core’s OIDC middleware, which previously operated in the in-memory SessionStore mode. In this mode, the Identify Admin only transmitted the session ID through the .AspNetCore.Session cookie key of the authentication session to the client-side. However, this approach only functioned effectively with sticky sessions since the key was used to retrieve the complete cookie data from the servers’ memory. To address this limitation, we have reconfigured the system to transmit the entire content of the .AspNetCore.Session cookie to the client-side.
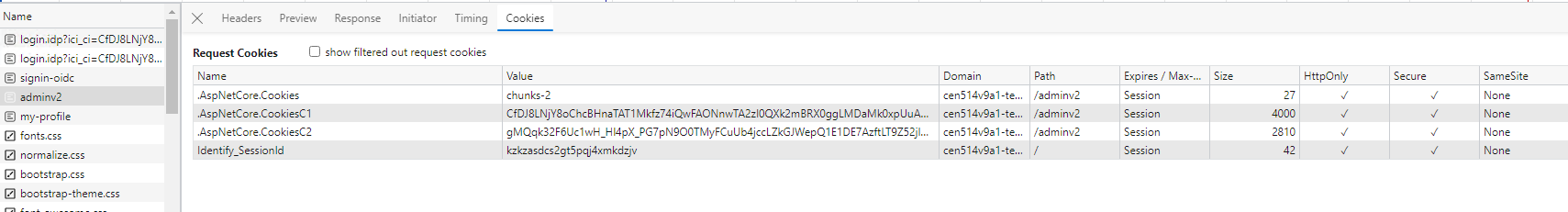
Before the change:

After the change:
The second change above has significant implications that led to the third change. While a session ID is just a short string, the entire content of the .AspNetCore.Session cookie is large, resulting in increased size for all Identify’s cookies.
When logging in to the Identify Admin using a Username & password connection, the following cookies are sent to the Identify Admin:
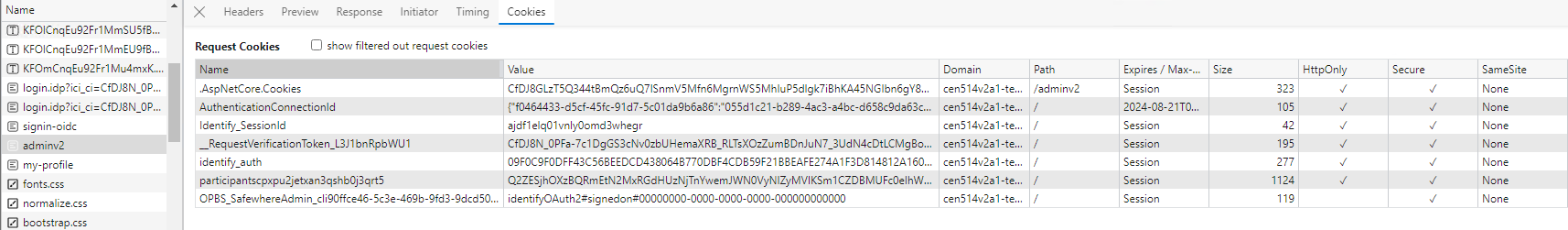
As you can see, all cookies of the Identify Runtime are sent to the Identify Admin because their paths are set to the root (/) path. When the total size of these cookies exceeds a limit, users may encounter the “HTTP Error 400. The size of the request headers is too long” error.
To mitigate the potential issue above, we have updated Identify Runtime to move all its large cookies to the /runtime path. The cookies that have had their paths changed are:
- AuthenticationConnectionId
- identify_auth
- participants[…]
- OPBS_[…]
- __RequestVerificationToken_[…]
- RememberChoiceTemp

One issue remains: for the cookies that were changed to the new path, if a browser already has those cookies set before the upgrade, there will be two cookies with the same keys. Therefore, Identify Runtime has a new guard that checks if more than one cookie with those keys is submitted, and it deletes the ones at the root path.
Impacted code
This feature requires code changes of the following modules:
- REST API: No changes
- Configurator: Deploy encrypted connection strings for Identify Admin.
- Identify Admin portal: Changes in how cookies are stored and protected.
- Identify Runtime: Changes to the path of many cookies and cleanup of old cookies.
New setting to execute HRD rules when selecting the ‘Return to selector page’ link
Before version 5.15, selecting Return to login selector page always directed the user back to their login page, regardless of the current applied HRD configuration on the service provider, like domain-based HRD. However, we have introduced a new setting called HRD:SuppressForceShowLoginChooserAndRunHRDPipelineInstead, which allows you to customize the HRD behavior in Identify. With this setting, HRD is forced to run again whenever users choose the Return to login selector page link.
To enable this option, simply add an additional connection setting with the following configuration:

Security review
We’ve improved our system based on valuable customer feedback and vulnerability scanning results:
- Patched high/critical vulnerabilities in JavaScript components.
- Removed loading resources from external services like fonts.googleapis.com, cdnjs.cloudflare.com, gravatar.com, and inlinemanual.com.
Identify Admin
New Usability on Identify Admin
Some small improvements are:
- Reformulate the question in the “Leave?” popup message from “Do you want to save your changes” to “Do you want to discard your changes”, and update the labels of the two buttons to: “Stay on page” / “Leave without saving”

- Update the input field description for the search list, e.g., the clam list. When used for filtering on the current page, the text label prefix should be “Filter by…”. When used for searching within the database, the text label prefix should be “Search by…”.
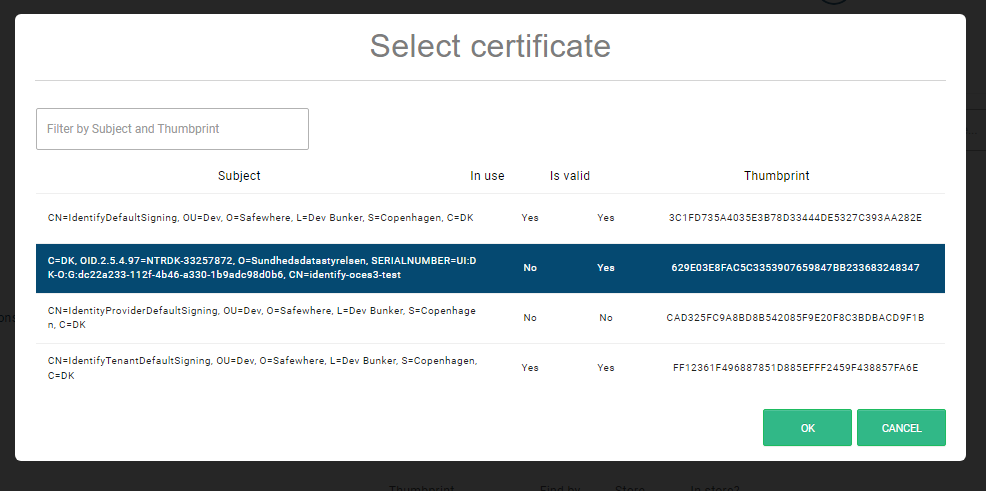
- You can now filter certificates by subjects and thumbprints on the Certificate Search dialog.
- Show an error message on the Script library page when trying to add the wrong value format on the Additional namespaces or Additional reference assembly.

- Update new document links on the System information.
New updates on SMS Gateway
Our latest SMS gateway improvements empower you to create personalized messages effortlessly and enhance security with modern APIs. Let’s explore the updates:
- URL Support for GET Method: Some SMS providers now use a specific method to send messages, requiring details like recipient, subject, and body in the URL. With our latest update, you can now easily personalize your SMS content using simple merge fields like
<%=SMSNUMBER%>,<%=SMSTEXT%>, and<%=SMSBODY%>directly in the request URL setting. - Enhanced Security for Modern APIs: SMS providers are moving towards modern APIs with enhanced security. They now use API keys in headers instead of usernames and passwords. This approach offers increased security as headers are rarely logged, unlike the URL.
Visit the SMS gateway settings for configuration and testing using the HTTPRequest SMS gateway.
Diagnostic and monitoring tool
The Diagnostic and monitoring tool is a brand new tool designed to help you diagnose various metrics related to your Identify instances. It provides insights into your database size, data table size, existing indices, missing indices, and offers the option to clean up data from the OAuthAccessToken and AuditOAuthAccessToken tables. Additionally, it warns you if your Identify instance lacks second-factor authentication for the Identify Admin login or if the signing certificates are nearing expiration. We strongly recommend running the tool on your Identify instances before performing an upgrade from an old version to the latest version.
Breaking changes
When upgrading Identify instance from a previous version, you may experience some changes:
Changes in Razor views and Hosted forms
The Site Layout template is updated due to external link removal. Please refer this pull request for more details about the change. If you are using Hosted forms, you can now safely remove the corresponding line from your customized Site layout. As a side note, the external link will continue to function if you prefer not to make any changes at this time.
Identify Runtime’s cookies have been updated to the new path
All changes in the Identify Admin and load-balancing section should not cause any breaking changes, unless you have custom code or a network setup that depends on the previous behavior of all Identify Runtime’s cookies being set to the root path. Nonetheless, these are significant changes, and it is essential to test them thoroughly before deploying to production.
5.15 REST API change
You can find new changes on 5.15 APIs here.
5.15 known issues
You can find known issues of version 5.15 here.
Bug fixes
- Fixed: #96595 [IC] The DefaultLanguage setting in IdentifyMe’s appsettings.json is empty after the tenant upgrade
- Fixed: #93450 [IC] Cannot import Identity providers or Applications to Identify when their certificates are expired
- Fixed: #96633 [IC] Tenant upgrade/import/export/reconfiguration using the Configurator returns an error when the tenant uses a signing certificate in Windows Certificate store and its public key is not imported to LocalMachine\TrustedPeople.
- Fixed: #102204 [CLI] Signing thumbprint information is logged in the CLI log when it validates the SSL certificate information
- Fixed: #102207 [CLI] The defaultLanguage value and clientName value of an upgraded tenant are changed to those from the Configurator.txt file
- Fixed: #101729 [IC] Can update the Multi-subnet failover setting during the Identify instance replication
- Fixed: #101030 [IC] Documentation link is out-of-date on a few Identify Configurator steps
- Fixed: #100927 [IC] The EncryptionRecoveryPassword is not hidden on Identify log
- Fixed: #88193 [IC] Remove the old warning on the Identity Configurator when replicating the tenant that uses InProc session state.
- Fixed: #96466 [Runtime][HRD] User is asked to re-enter his or her user name or email on the Domain-based HRD’s page when the input value contains spaces
- Fixed: #98097 [Runtime][SAML] “Could not read Response. A wrong encoding is most likely being used.” has been returned on the service provider when the IncludeSamlStatusErrorMessage setting in the Runtime web.config is set to true, and the status message contains special characters
- Fixed: #99490 [Runtime][OAuth20] The devicecode value and usercode value are not logged in the AuditDeviceAuthorizationResponse table
- Fixed: #102071 [Oauth20] “Audience validation failed” is logged in the Runtime log when calling the registration_endpoint to register a dynamic application, in case the Identity Entity ID is customized
- Fixed: #101948 [Runtime] Some Danish text resources for WebAuthnFirstFactor are not translated
- Fixed: #92373 [LinkedIn] Users encounter The application is disabled message when using the LinkedIn provider
- Fixed: #91978 [STS] Object reference not set to an instance of an object is returned when Use database certificate revocation checks is enabled and client certificate does not exist on database store
- Fixed: #101923 [Runtime] The id_token contains the system claims when the id_token is set on the User claims placement and the logged user comes from an upstream Identity Provider
- Fixed: #96707 [OAuth20][BasicAuthentication] Cannot exchange the access token when the Client secret contains a % character and the Token endpoint authentication method is ClientSecretBasic
- Fixed: #96377 [IdentifyAdmin] User cannot save the connector application/identity provider when it contains an expired certificate
- Fixed: #101719 [IdentifyAdmin] Cannot upload a certificate for the user after an error occurs
- Fixed: #96419 [IdentifyAdmin] Site Layout on the hosted form list cannot be reset to default after the first update.
- Fixed: #96377 [IdentifyAdmin] The connector application/identity provider that contains an expired certificate, such as Salesforce cannot be updated
- Fixed: #96374 [IdentifyAdmin] The WS Federation /WS Trust application that contains an expired certificate on Received Security Token Encryption certificate can not be updated
- Fixed: #96351 [IdentifyAdmin][Certificates] Allow search by thumbprint when there are spaces between certificate thumbprint
- Fixed: #96238 [IdentifyAdmin] The unique domain validation is missing when inputting a value in the Domain-based filter for the HRD field during the Identity provider update
- Fixed: #93017 [IdentifyAdmin] English typos on IdentifyAdmin page
- Fixed: #92509 [IdentifyAdmin] The link attached in the correlation report mail uses an obsolete URI to the old admin.
- Fixed: #91982 [IdentifyAdmin] Saving System settings has still returned a strange error after a validation error message displayed and you corrected it
- Fixed: #96657 [IdentifyAdmin] Cannot rename Group from uppercase to lowercase and vice versa
- Fixed: #96650 [IdentifyAdmin] The HTML tag <br/> is included in the error message when the script fails to compile
- Fixed: #99108 [IdentifyAdmin] “Sorry, the connection name cannot be changed” has been returned when re-updating the metadata URI on the SAML IdP-Initiated application
- Fixed: #96958 [IdentifyAdmin][SAML20] Single log off service POST setting is displayed on the Connection tab when inputting Single Sign On service in the search field
- Fixed: #101674 [IdentifyAdmin] The Filter claim types condition and the Filter by claim type condition cannot be applied simultaneously in the Uniqueness list
- Fixed: #90726 [IdentifyAdmin] The search field on the Connection tab of the OIDC Application is missing
- Fixed: #100078 [IdentifyAdmin] Typo in menu text on the System Information list
- Fixed: #101581 [IdentifyMe] The reset password is appended to the reset/change password link when performing a password reset on the reset/change password page
- Fixed: #91856 [IdentifyMe] Improve UX of the Recovery code page on the WebAuthn authenticators and the TOTP authenticators
- Fixed: #96599 [IdentifyMe] Cannot change to Danish language
- Fixed: #97908 [Swagger] Documentation for the PATCH method on the API: api/rest/v2/lockedusers is out-of-date
- Fixed: #90458 [RESTAPI] Identity bearing claim can be configured via REST API when only WebAuthn is set as the Second factor method(s) and Use as the second factor only is enabled
- Fixed: #100113 [RESTAPI] Can delete the default SMS gateway on the API: api/rest/v2/smsconfiguration/smsgateway/{name}
- Fixed: #97239 [IdentifyAdmin][Runtime] Improve performance, resource management, and consistency on the OTP plugin when updating its components’ lifestyle from Transient to Singleton.
- Fixed: #97207 [Runtime] Correct the registrations on the Home Realm Discovery rule module.




